Which Activity Manages The Baseline Settings For A System Or Device?
Which activity manages the baseline settings for a system or device?. Defaults for one baseline might not match defaults from other security baselines or from other versions of this baseline. The tool includes both signature and anomaly monitoring methods. Winning medical device startups have a few factors in common according to McKinsey research.
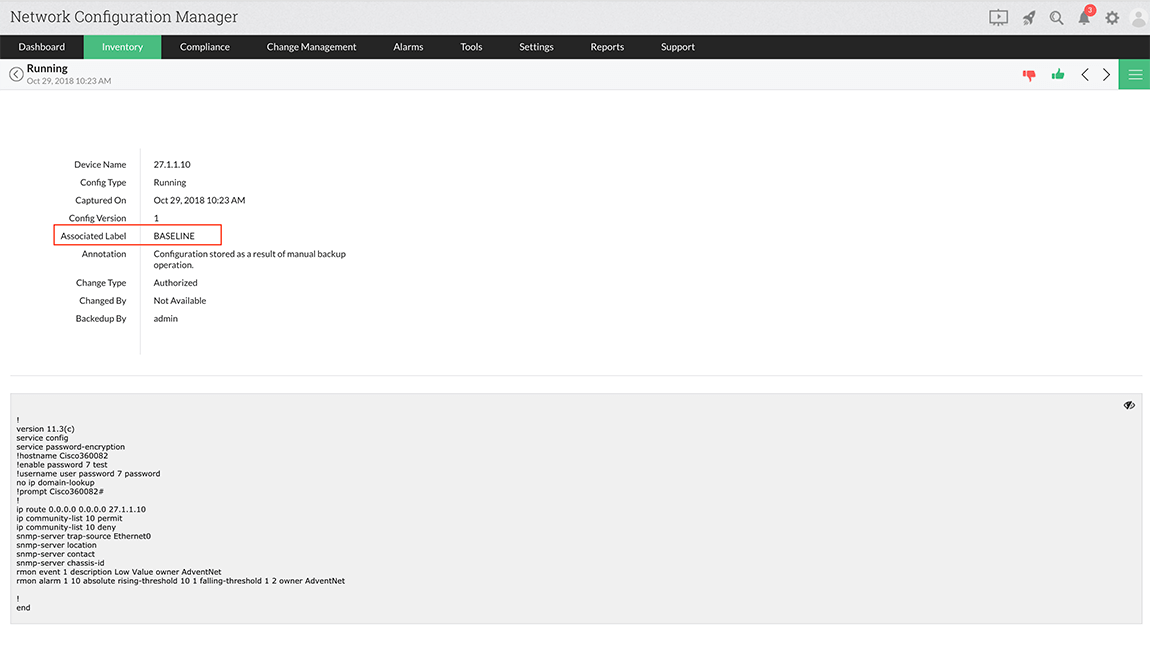
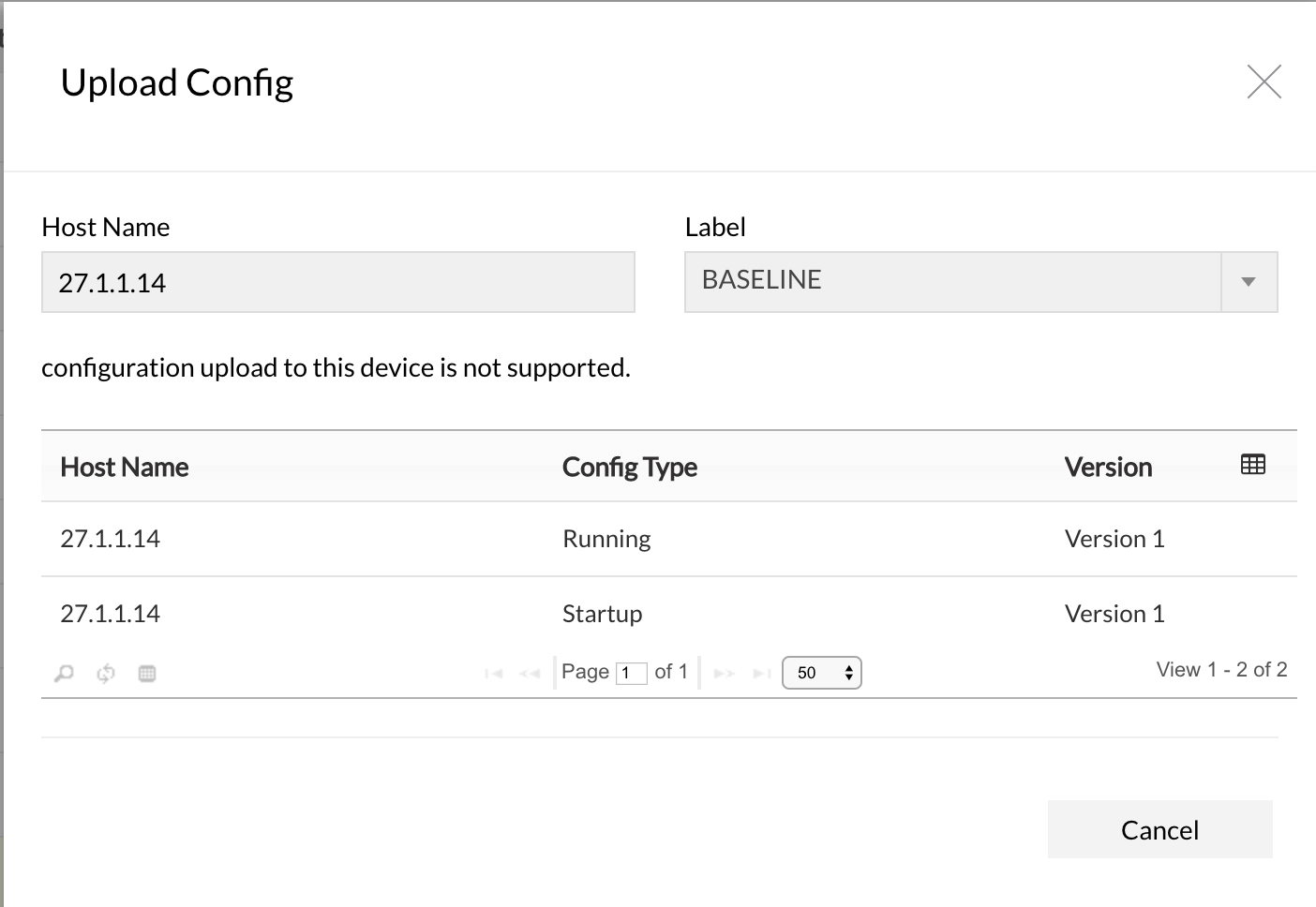
SolarWinds Network Configuration Manager FREE TRIAL. Asked Sep 30 in Other by megha00 Expert 349k points 0. Stopping or disabling the WcsPlugInService service will disable this extensibility feature and the Windows Color System will use its baseline model processing rather than the vendors desired processing.
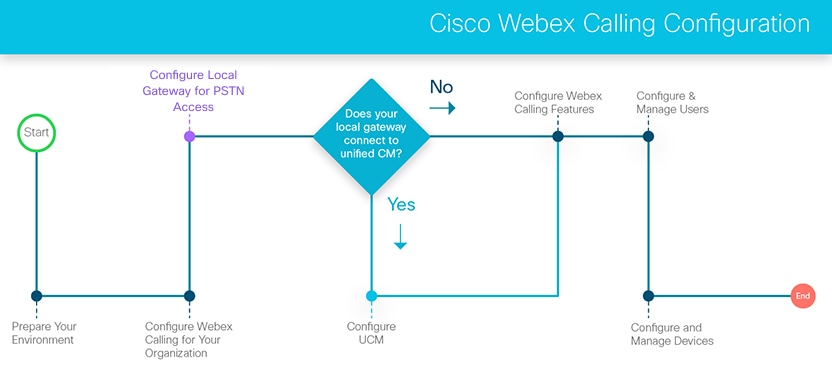
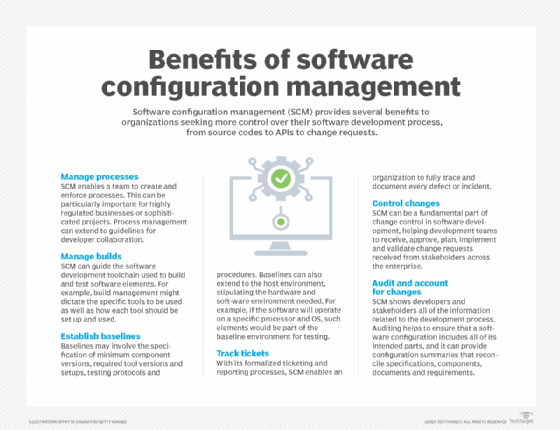
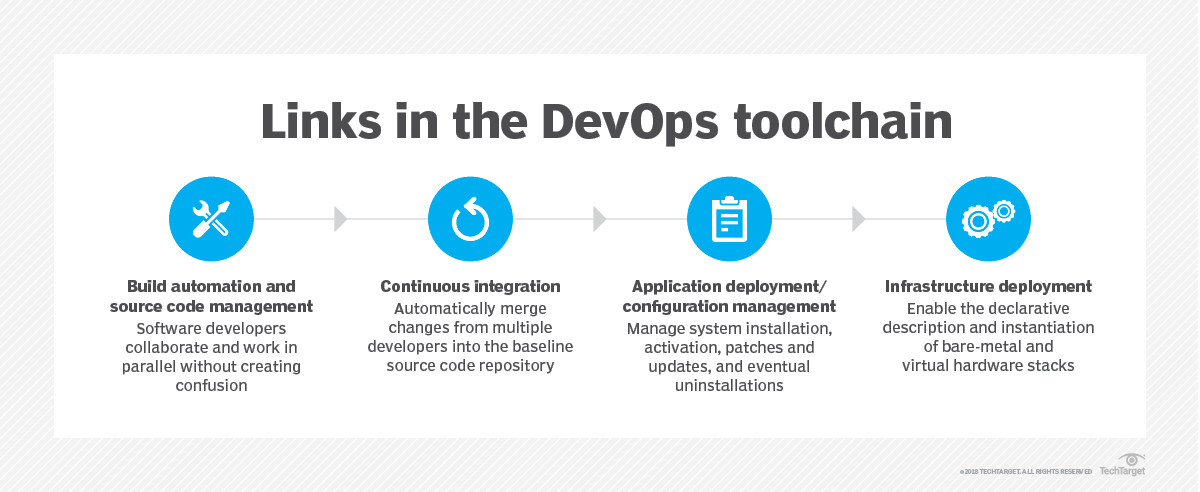
And configuration settingsparameters network. After setting it to 1 there is no red wordings Some settings are managed by your organization. Baseline configurations include information about information system components eg standard software packages installed on workstations notebook computers servers network components or mobile devices.
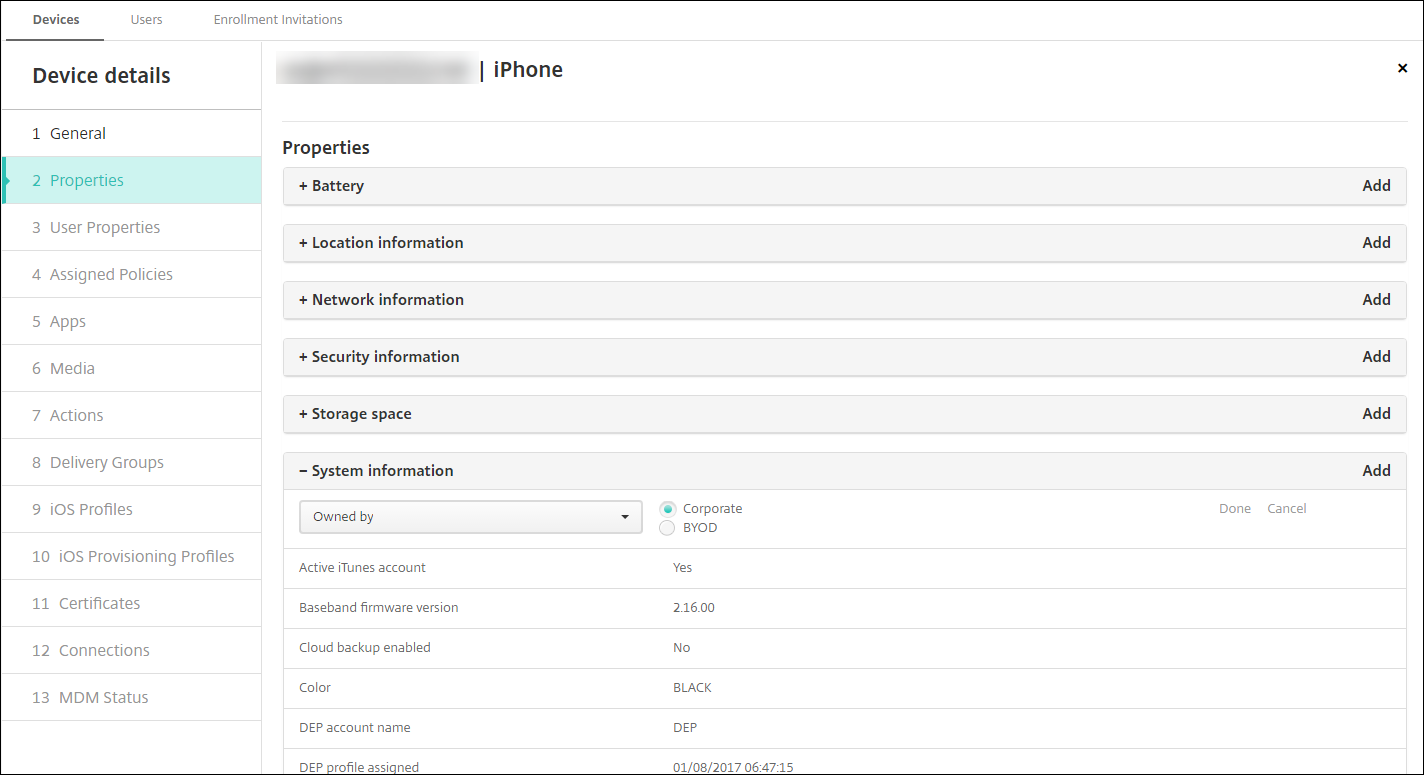
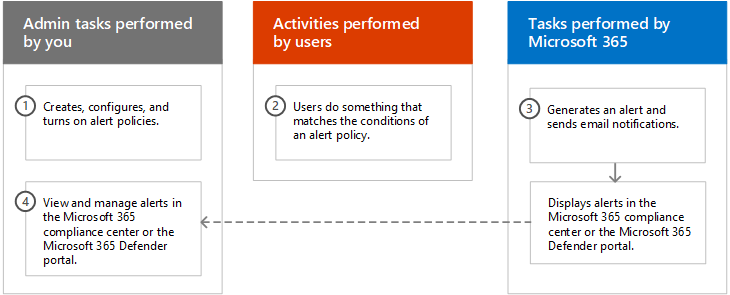
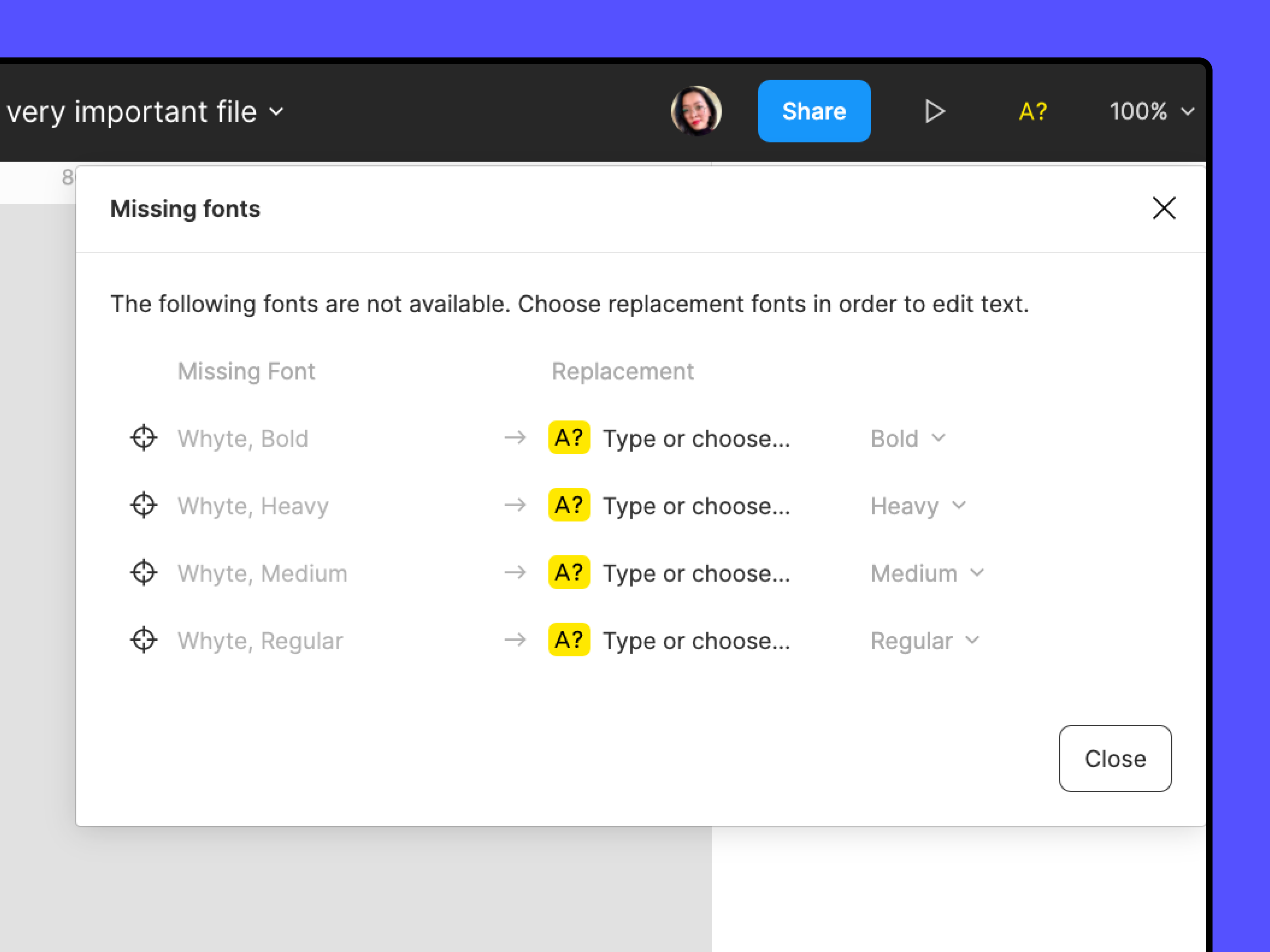
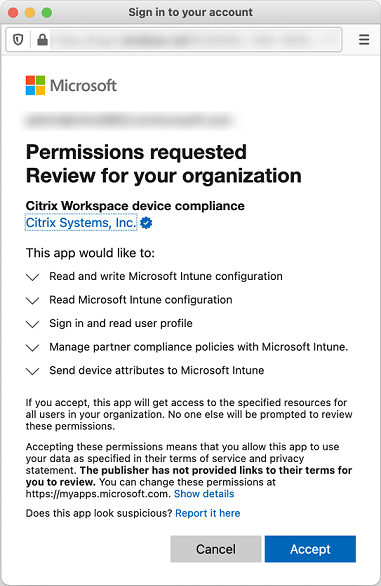
When it detects abnormal activity on a device zIPS sends the user an alert and blocks malicious activity like stopping a phishing link from loading. If you are trying to figure out how to apply group policies on and off the domain enforce those policies offline track compliance use inbox or application AMDX policies and dont know where to start in VMware Workspace ONE UEM aka. This Windows 10 operational tutorial covers the benefits and all the steps to consider when moving to cloud-based group policies and other configurations.
Baseline configurations include information about information system components eg standard software packages installed on workstations notebook computers servers network components or mobile devices. The Top 10 Medical Device Startups in 2021. Asked May 9 in Other by gaurav96 Expert 689k points 0 votes.
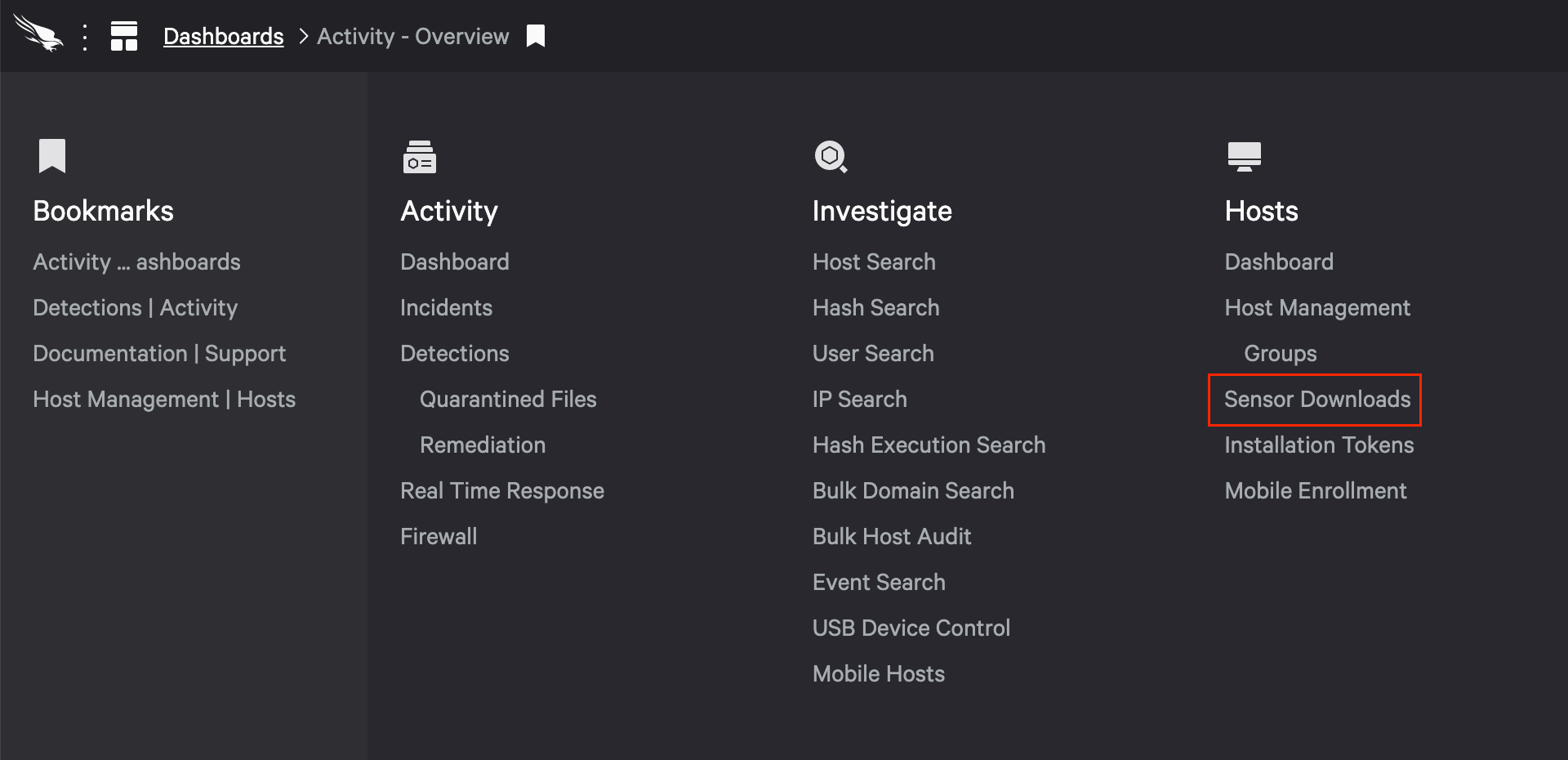
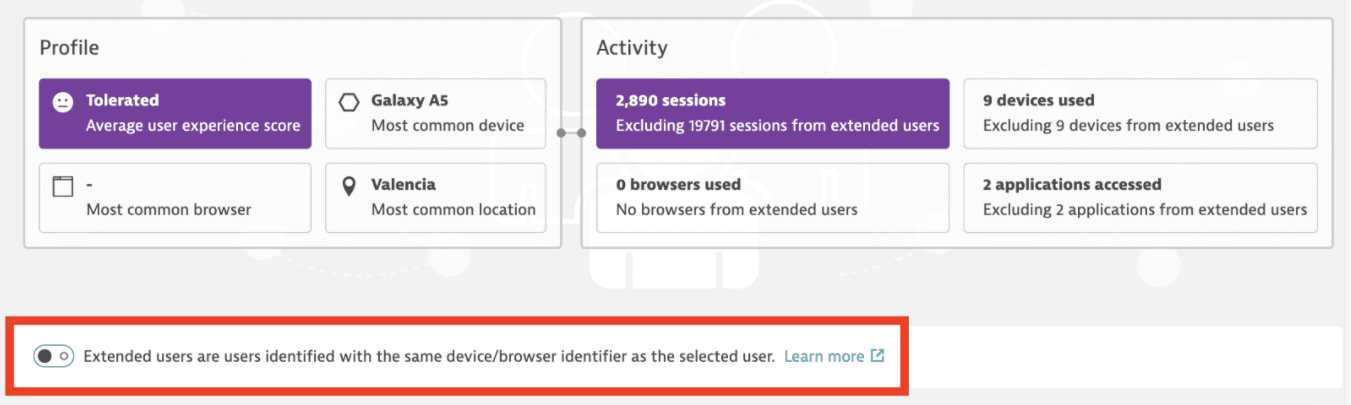
The Best Employee Monitoring Software for 2021. Use Azure Firewall to send traffic and centrally create enforce and log application and network. As this is a command-line function.
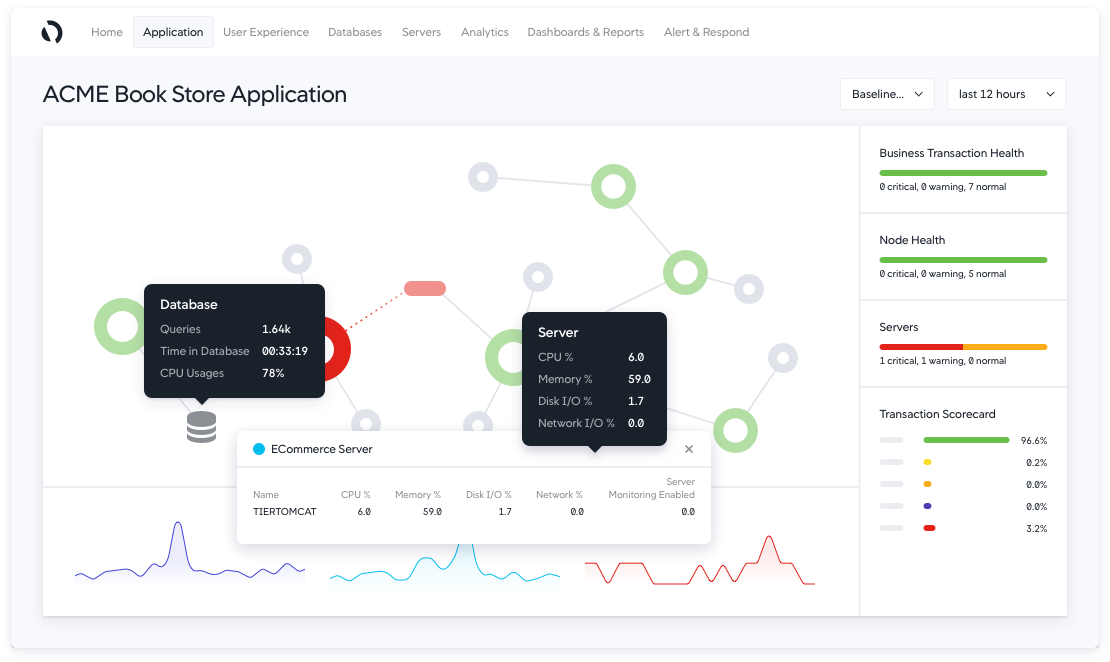
This provides added security for the credentials that the LSA stores and manages. Monitor and log the configuration and traffic of virtual networks subnets and network interfaces.
The Baseline Domain Security Policy should contain settings that apply to the entire domain.
The Top 10 Medical Device Startups in 2021. It is only free for an evaluation period and covers a particular but important subset of vulnerabilitiesNCM handles both vulnerability scanning and management for the domain of vulnerabilities arising from the router and switch misconfiguration. Instead now there is a Update Settings in Settings and it still says Available updates will be downloaded and installed automatically except over metered connections where charges may apply. This device manages traffic leaving one network and bound for another. Current version numbers and patch information on operating systems and applications. If you are trying to figure out how to apply group policies on and off the domain enforce those policies offline track compliance use inbox or application AMDX policies and dont know where to start in VMware Workspace ONE UEM aka. View the security baseline settings that Microsoft Intune supports for devices that run Windows 10 and Windows 11. Current version numbers and patch information on operating systems and applications. The tool includes both signature and anomaly monitoring methods.
When you are done the system will automatically calculate for you the amount you are expected to pay for your order depending on the details you give such as subject area number of pages urgency and academic level. Stopping or disabling the WcsPlugInService service will disable this extensibility feature and the Windows Color System will use its baseline model processing rather than the vendors desired processing. Current version numbers and patch information on operating systems and applications. Which of the following kinds of software is not usually included by an installed operating system. These plug-in modules are vendor-specific extensions to the Windows Color System baseline color device and gamut map models. When it detects abnormal activity on a device zIPS sends the user an alert and blocks malicious activity like stopping a phishing link from loading. When you are done the system will automatically calculate for you the amount you are expected to pay for your order depending on the details you give such as subject area number of pages urgency and academic level.

























Post a Comment for "Which Activity Manages The Baseline Settings For A System Or Device?"